Data Treatment and Privacy Notice
Thank you for using Truora!
We have a dedicated privacy team that is committed to protecting all the personal data we collect and ensuring that it is handled correctly in every country we serve. Please carefully read our DataTreatment and Privacy Policy (hereinafter the "Privacy Policy"). In order to use our site and receive the services we provide, you must read and accept this Privacy Policy, as well as our Terms and Conditions available at www.truora.com.
1. Introduction and Objectives
This Privacy Policy is the document that regulates the administration of all Databases and/or files of Truora, which contain Personal Data, of clients, contractors, suppliers and third parties in general, that are subject to Treatment by Truora, in the events in which it is considered as "Processor" and/or "Controller" of the Treatment of said Personal Data, in accordance with the provisions of the Statutory Law 1581 of 2012, Decree 1377 of 2013, External Circular No. 02 of November 3, 2015 and other regulations that modify and/or add them from now on. Likewise, it aims to establish the policies and procedures for the management and protection of information for Truora in line with the Information Security Policy implemented by the company, in order to preserve security in the exchange, transfer or destruction of information.
2. Definitions
- Authorization: Refers to the prior, express, and informed consent of the Data owner to carry out the Processing of personal data.
- Associated and/or Related: Corresponds to our parent company, affiliates, related, subsidiaries, allies, and subordinates.
- Biometric Data: Refers to the following data: fingerprints, facial recognition, iris recognition, autograph signature recognition, voice recognition.
- Controller: means the natural or legal person, public authority, agency or other body which, alone or jointly with others, determines the purposes and means of the processing of Personal Data.
- Database: Refers to the organized set of Personal Data that is subject to Treatment.
- Data Owner: Corresponds to the owner of the information, it can be a natural or legal person whose Personal Data is subject to Treatment.
- Data Transfer: The transfer of data takes place when the Processor and/or Controller for the Processing of personal data, located in Colombia, sends the information or personal data to a receiver, who in turn is Controller for the Treatment and is located in or out of the country.
- Deleted Data: Refers to the data for which the express authorization of the Data Owner could not be obtained to carry out its treatment or that, at the request of the Data Owner, its elimination is required or those that Truora decides to eliminate from its Databases.
- Privacy Notice: Refers to the verbal or written communication addressed to the Data Owners of the personal data being processed by Truora, in which they are informed about the existence of the personal data processing policies that will be applied to them, the way to access them, and the purposes for which your personal data will be used.Database: Refers to the organized set of Personal Data that is subject to Treatment.
- Personal Data: Refers to any information linked or that may be associated with one or more specific or determinable natural persons; to information provided by any natural or legal person who registers on our website and/or mobile applications.
- Public Data: Refers to the data qualified as such by virtue of the law and that is not semi-private, private, or sensitive. It’s considered public data, among others, the data related to the marital status of people, their profession or trade, their quality as a merchant or public servant and those that can be obtained without reservation. By its nature, public data may be obtained, among others, in public records, public documents, official gazettes and bulletins.
- Private data: It is the data that, due to its intimate or reserved nature, is only relevant to the Data Owner.
- Processor: means a natural or legal person, agency or other body which processes Personal Data on behalf of the controller, exclusively for the fulfillment of the commercial relationship on behalf of and under the instructions of the Controller.
- Sensitive Data: Sensitive data is understood as that which affects the privacy of the Data Owner or that when subject to improper use may affect the privacy of the Data Owner or that has the potential to generate discrimination, such as those that reveal racial or ethnic origin, political orientation, religious convictions or philosophical beliefs, membership in trade unions, social or human rights organizations or that promote the interests of any political party or that guarantee the rights and warranties opposition political parties, as well as data related to health, sexual life and the biometric data.
- Treatment: Any operation or set of operations on Personal Data, such as the collection, storage, use, circulation, or deletion of the same.
- Truora: Means as a whole, all the companies that belong to the Truora Group, that is: Truora S.A.S. identified with the TIN No. 901.189.979-5, Truora Fraud Prevention identified with the RFC: TFP 191219TG0, Truora Chile SpA identified with the RUT No. RXW 77.140.321-2 and Truora Tecnologia LTDA identified with the CNPJ No. 34.785. 867/0001-11.
3. Treatment and Scope of Personal Data
Truora, in the development of its corporate purpose and economic activity, acts as the person Processor and/or Controller for the processing of Personal Data provided by clients, employees, contractors and/or suppliers, which will be stored in its databases and in those of who by virtue of this policy may access them.
Consequently, Truora collects, stores, uses, transmits, transfers, deletes and in general treats the Personal Data provided by natural and legal persons with whom it has or has had some type of relationship, whatever its nature (civil, commercial and/or labor); which includes, but is not limited to, clients, cloud software users, allies, suppliers, contractors, workers, creditors, debtors, and shareholders.
This document covers the treatment of the information managed in Truora. It covers all deliveries, transfers, or assignment of information and/or data of medium or high confidentiality both within the organization and with the cloud of clients, suppliers, external databases, social networks, and the general public.
Information exchanges can occur through the use of various types of communication, be it verbal, face-to-face or telephone conversations, visual, video, or written, on paper or digital media. It involves the collection, transfer, processing, storage, and deletion of the information provided by clients.
4. Guiding Principles
We are committed to ensure that any Processing of Personal Data that we carry out always respects the rights enshrined in our Constitution and in the laws. Therefore, the following are the principles that guide our behavior:
- Principle of quality: Truora seeks that the Personal Data Processed are accurate, complete, pertinent, correct and up to date, in order to comply with the necessary purposes indicated in the comprehensive privacy notice.
- Principle of confidentiality: All persons involved in the Processing of Personal Data are obliged to guarantee the confidentiality of the information, even after the end of their relationship with any of the tasks that such processing comprises.
- Principle of consent: Truora obtains consent for the Processing of Personal Data in a free, specific, and informed manner, except when it is not required in accordance with article 10 of the LFPD.
- Principle of information: Truora provides complete information regarding the Personal Data it processes, and other requirements established by the LFPD so that you can exercise your rights of informative self-determination, privacy, and protection of personal data.
- Principle of purpose: The Processing of Personal Data must obey a legitimate purpose that will be reported to the Data Owner.
- Principle of freedom: The Processing of Personal Data can only be exercised with the prior, express, and informed consent of the Data Owner.
- Principle of legality: Truora obtains the data in accordance with the applicable legislation both in Mexico and internationally.
- Principle of loyalty: Truora does not use deceptive or fraudulent means to collect Personal Data and treats it at all times in good faith and with the utmost diligence regarding the information provided by clients and users, maintaining reasonable expectations of respect for the privacy of the Data Owners, in the understanding that we will carry out the treatment of their data in accordance with what was agreed.
- Principle of proportionality: Truora only Processes the Personal Data that is necessary, appropriate, and relevant for the purposes indicated in our comprehensive privacy notice.
- Principle of responsibility: Truora has established policies and procedures for handling Personal Data within its organization that are mandatory and in accordance with the best international practices that allow the Treatment of Personal Data to be carried out responsibly. Likewise, it carries out the training, updating and awareness of the personnel regarding the applicable provisions and obligations of the protection of Personal Data and have established internal supervision and surveillance systems to verify compliance with the policies that are reviewed periodically to determine if some modification is necessary.
- Principle of security: The information subject to Treatment must be handled with commercially reasonable technical, human, and administrative measures, which are necessary to provide security to the records, avoiding their adulteration, loss, consultation, use or unauthorized or fraudulent access.
- Principle of veracity: The information subject to treatment must be truthful, complete, exact, up-to-date, verifiable, and understandable. The Treatment of partial, incomplete, fragmented, or misleading Personal Data is prohibited.
5. Use of the Privacy and Information Protection Policy
All Processing of Personal Data will be subject to this Privacy Policy, therefore, if a Data Owner does not agree with this Privacy Policy, he or she will not be able to provide any information that must be registered in one of the Truora Databases.
Truora, is committed to the security of the Data that is supplied to it and, consequently, undertakes to give it the appropriate use, as well as to maintain the confidentiality required in relation to it in accordance with the provisions of this Privacy Policy, and in the existing legislation on the matter. In accordance with what is established in this document, at the moment in which the Data Owners submit their Personal Data to be collected in Truora's Databases, it is understood that said Data Owners accept and know that the Treatment of said Personal Data will be subject to this Privacy Policy.
The Personal Data may be transferred to its shareholders, Associate and/or Related Parties, as well as to third parties and to judicial or administrative authorities, whether natural or legal persons, Colombian or foreign, in those events in which the transfer or transmission of the data is necessary to carry out the uses and activities authorized by the Data Owners in accordance with the corporate purpose of Truora. In all events, the exchange of said information must be subject to the requirements established in section 6 of this Policy. Likewise, the information must be kept under strict confidentiality and will be subjected to rigorous Treatment, respecting the rights and guarantees of its Data Owners.
Truora may use service providers and data processors working on its behalf. Said services may include system hosting and maintenance services, encryption, analysis services, email messaging services, call center services, delivery services, payment transaction management, and solvency and address controls, among others. Consequently, the Data Owners understand that by providing information to Truora, they will automatically be granting these third parties authorization to access their Personal Data.
Therefore, Truora undertakes to take all necessary actions to ensure that both service providers and processors working on behalf of the company and other authorized third parties in accordance with this Privacy Policy, protect, in all events, the confidentiality of the Personal Information in its care.
Truora may collect information that is in the public domain to supplement the Databases. Said information will be given the same treatment indicated in this Privacy Policy.
6. Disclaimer
Truora makes its best efforts to comply with the current regulatory provisions to safeguard the information that the Data Owners have provided or that the clients have transmitted to it, however, it is possible that on the occasion of an unforeseen external attack in which a breach in the security is opened or in the databases that protect the information, the information can be lost or leaked. Considering the foregoing, the Data Owners declare that they understand the risk involved in disclosing, sharing, or allowing access to information by electronic means and therefore exonerate Truora from any responsibility when unforeseen situations violate the rights of the Data Owners of the information.
7. Effects of the Authorization
It is understood that the Authorization granted by the Data Owners is an express and informed authorization granted by them in favor of Truora, its Linked and/or Related Parties and third parties determined by Truora by virtue of the development of its corporate purpose, to treat the Personal Data, regardless of the means (written, oral or through unequivocal conduct) by which they were delivered. Likewise, it implies the understanding and full acceptance of all the content of this Privacy Policy.
In the event of a sale, merger, consolidation, change in corporate control, transfer of assets, reorganization, or liquidation of Truora and/or its Linked and/or Related entities, Truora may transfer the Personal Data of the Data Owners to the parties involved for which by accepting this document Truora is understood to be empowered to do so.
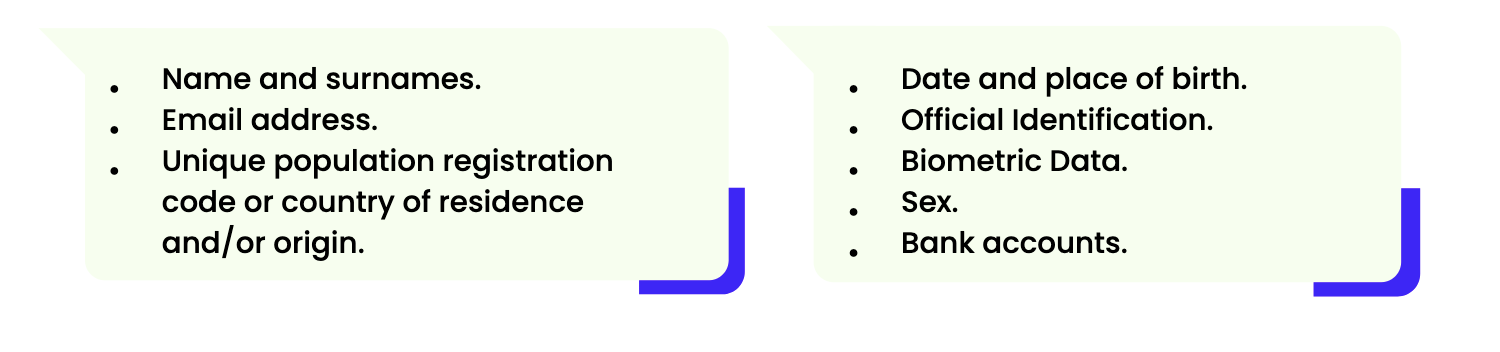
8. Personal Data Subject to Treatment
Truora collects or receives information and Personal Data that falls into the following general categories.
Data from Minors: Truora´s websites and applications are not directed to minors or those under 18 years of age. Truora does not knowingly collect any personal information directly from anyone under the age of 18. If you believe that we have processed personal information relating to a minor inappropriately, we encourage you to contact Truora using the information provided in the "Contact Us" section below.
Data in publicly accessible sources: Truora obtains data through remote or local means of electronic, optical, and other communication technologies in publicly accessible sources, that is, stored in sources that anyone can access and that include telephone directories, newspapers, gazettes, official bulletins, and social communication media, all in accordance with the applicable regulations. Therefore, Truora does not require consent to obtain personal data from publicly accessible sources.
9. Purposes and uses of the information
The personal data that is supplied to Truora will be given a Treatment in accordance with the following purposes for the use of the information, as applicable to each Data Owner:
- The correct execution of the contract formalized between the Data Owner and Truora.
- Account creation for the access to the Truora Platform
- Verification of identity with any current official document that serves to prove identity.
- Facilitation of contact between Truora and the Data Owner.
- Improvement of Truora's commercial and promotional initiatives, as well as analysis of the pages visited and searches carried out, to improve Truora's offer of content and articles, and customization of said content, its presentation, and services.
- Development of measurement studies regarding the participation of different sectors of the population in Truora.
- Sending information or text messages to the supplied cell phone, email, about new services, changes in the service and rates, payment reminders, promotions, events, and information of interest to the Data Owners in general.
- Billing and other tax effects, in which case it will be shared with the State entities responsible of carrying out said work.
- Analysis of Personal Information by Truora, its shareholders, Affiliates and/or Related Parties and third parties contracted for the development and promotion of the sale of its services.
- Complete the profile information on the Truora Platform.
- Payment processing of services purchased.
- Identity validation
- Compilation of the services that the Data Owners use and the way in which they use them.
- Obtain information from other sources and combine it with the information Truora collects through the Truora Platform.
- Review of police, criminal, or sex offender listing history.
- Review of Fraud Detection and Security Issues.
- Receipt of criminal background check results or fraud warnings from identity verification services for purposes of Truora's fraud prevention and risk assessment efforts.
- Reception of information about the Data Owner, his activities inside and outside the Truora Platform through its partners or information about the experiences and interactions that the Data Owner has had through our network by associated advertisers.
- Other communications and activities related to the corporate purpose of Truora.
10. Duties and rights of the Data Owners
The Data Owners of the Personal Data provided to Truora will have the following rights:
- The right to know, update and rectify your Personal Information free of charge.
- The right to request proof of the existence of the authorization granted to Truora, except when expressly except in the law as a requirement for Treatment.
- The right to be informed, upon request, regarding the use that has been given to your Personal Information.
- The right to present before the Superintendence of Industry and Commerce or the competent authority, complaints for violations of the provisions of the current Law and the other regulations that modify, add, or complement the same.
- The power to revoke the authorization and the request for the deletion of the data when it is not used in accordance with the authorized uses and purposes. The revocation and/or deletion will proceed when the Superintendency of Industry and Commerce or the competent authority has determined that in the Treatment, Truora has incurred in conduct contrary to the law.
- The right to submit queries and claims regarding Personal Data.
The Data Owners of the personal information provided to Truora will have the following duties:
- The duty to provide truthful information, which can be verified by Truora for control and validation purposes. Truora will have the power to deny requests when it is verified that the information provided by the Data Owner is false or has inconsistencies.
- The duty to keep the contact information up to date, in order to ensure a more efficient and timely provision of the service, in addition to allowing a direct communication and information channel between Truora and the Data Owner.
11. Confidentiality of Personal Data
Personal Data provided by the Data Owners will be used only by Truora, its shareholders Owners, Linked and/or Related Parties and authorized third parties for such purposes, in accordance with the provisions of this Privacy Policy. The Data will not be used, in any event, for purposes other than those for which they were provided, which is why Truora will protect the privacy of Personal Information and will make its best efforts to keep it under the necessary security conditions to prevent its adulteration, loss, consultation, unauthorized or fraudulent use or access, as well as the respect for the rights of the Data Owners of the same.
If for any reason a competent authority requests the disclosure of Personal Information, which is in Truora's possession, and, consequently, it is its legal obligation to supply it, Truora will proceed to deliver said Information, a situation that the Data Owners accept and authorize Truora for this purpose, in any case the Data Owner of said information will be informed.
12. Information Security
In compliance with the provisions of the Federal Law on Protection of Personal Data Held by Private Parties (in the case of Mexico), Statutory Law 1581 of 2012 (in the case of Colombia), the Lei Geral de Proteção de Dados Pessoais (in the case of the case of Brazil), Law 19,628 (in the case of Chile), the "General Data Protection Regulation or GDPR, and other legislation, international treaties, decrees, circulars, manuals, recommendations and/or relative and applicable regulations on Protection and Privacy of Personal Data, Truora has implemented administrative security measures to establish at the organizational level, the management, support and review of the security of the Personal Data, the identification and classification of information, as well as the awareness, education and training of its personnel in matter of personal data protection. Likewise, Truora has established physical security measures using state-of-the-art technology to prevent unauthorized access, damage or interference to its physical facilities, critical areas, equipment, and information to protect mobile computing equipment from any unauthorized access and has also implemented technical security measures so that access to our databases is only made by authorized users. Therefore, in the event of a breach of your personal data, we will analyze the causes for which said breach occurred and we will implement the necessary corrective, preventive, and improvement actions to make the necessary security adjustments to reduce the risk of a new infringement.
Notwithstanding the foregoing and considering that the services provided by Truora are developed through the Internet and that personal information is collected in the same way, there may be illegal interceptions or violation of systems and databases by unscrupulous or unauthorized persons. In this event Truora is not responsible for the improper use of the information obtained by these means.
12.1. Information retention
The files that are under the responsibility of Truora must comply with the protocols and procedures established by the information security policy regarding asset management and information classification, in addition to complying with the following specifications:
-
- The data of the Data Owner will be stored in separate instances, with access controls for reading.
-
- Consultation of the information by unauthorized personnel must be avoided.
-
- All files are encrypted when they are stored in the designated repository.
-
- Transfers of sensitive or restricted files must be made through reliable messaging systems, where possible, with information encryption.
13. Media handling
Truora will implement procedures for the management of removable media in accordance with the classification scheme adopted by Truora. In any case, said procedures will correspond to the duties established below:
- Truora will destroy the media on which it stores confidential information when it is no longer needed for business reasons, such that the information is unrecoverable.
- Controls will be defined and implemented to protect the means with information that must be transported.
- Internal or external distribution of all types of media on which confidential information is stored will be strictly controlled.
- A classification of the means will be carried out in order to determine the confidentiality of the Data.
- Ensure all media moves are approved before moving from a secure area (including when media is being distributed to individuals).
- A detailed record of the inventory of all media will be kept.
- The use of mobile devices must be explicitly authorized, and they must comply with all policies, regulations and security standards defined in Truora, in order not to introduce risks within the corporate network.
14. Transfers and Referrals
Truora makes national and international referrals and transfers of your Personal Data under the terms of the comprehensive privacy notice and in compliance with applicable legal provisions, communications or referrals made between Truora and those responsible for data processing do not require consent. (Article 2, section IX of the LFPD Regulations) and some transfers that are made within the provisions of article 37 of the LFPD do not require it either, when any transfer requires your consent, said situation will be clearly indicated in our notice of comprehensive privacy policy, so we invite you to consult it in the link that appears at the end of our privacy policy.
14.1. Exchange of Personal Data.
When formal information exchange agreements are signed with third parties, Personal Data transfer procedures and/or protocols must be established that include the following security conditions as a minimum requirement:
-
- Establish responsibilities for control, delivery, and reception.
- Mechanisms to ensure tracking and non-repudiation.
- Establish responsibilities and obligations in the event of information security incidents, such as data loss.
- Establish contractual safeguards on the ownership of information, the care of personal data, respect for copyright, software licenses and similar legal considerations.
- Establish formal confidentiality agreements with recipients of information.
14.2. Collection of information in exchanges.
All information to be managed or processed by Truora and that is considered of high and medium confidentiality, or its equivalent, will be received in a format previously established for such transmission between Truora and its clients and/or suppliers, through secure and encrypted media, taking the following considerations:
-
- The exchange medium must be encrypted and have an authentication system, in addition to a medium access log.
- The transmission of the information must be done through a protocol that guarantees the encryption of the data at the moment of transmitting the information.
- The exchange medium must have access control limited by IP address, and only IP addresses previously informed by written communication from the Data Owner to the Data Owner of the information must be enabled.
- The deposited information must be stored in said means of exchange for a maximum of 24 hours. It is necessary to delete at least once a day all the information contained in the means of exchange.
- In the event that the Data Owner is unable to provide an information exchange media with the characteristics described above, the Grupo Truora may provide said media, complying with all the parameters described above.
- The use of the client´s or the supplier´s protocol that complies the highest level of security may be assessed.
- When information reception mechanisms are established, Truora will establish controls to prevent the entry of viruses or malware into its data network.
- The exchange of information via mail or instant messaging must be carried out in accordance with the guidelines and parameters established in this policy.
- In the event that data and/or confidential information is shared through telephone calls or video meetings, collaborators are required to take special care of when, where and how the information is shared or commented, to prevent it from being heard by unauthorized people or by the general public. If necessary, private places will be sought to prevent the disclosure of said information. If for any reason it is necessary to transport and/or store physical information, the packaging or file must be strong enough to protect the contents from any damage that may arise, in accordance with the corresponding environmental specifications, for example, to avoid damage due to heat or humidity and prioritizing the security of physical media through keys and the use of good practices.
14.3. Information loading
Information received through exchanges is processed through extraction, transformation and loading processes, considering the following specifications:
-
- Sensitive Data is previously encrypted before uploading the information to the Truora Group databases.
- Customer data must be stored in different databases.
- All databases are encrypted at rest.
- The extraction, transformation and loading processes should be executed in different instances.
- Validations of the integrity of the loaded data are carried out, considering the original base.
15. Cookies and other technological tools
Truora uses cookies and similar technologies to personalize and improve the customer experience, as well as to show you relevant online advertising. Cookies are small text files that contain a unique identifier that is stored on the computer or mobile device through which you access the website and/or mobile applications, so that they can be recognized each time you use the website and/or mobile applications. The Persona Data Owner can choose to disable some or all of the cookies we use at any time. However, this may restrict your use of the Sites and limit your experience of the Sites. The use of cookies does not contain or affect Personal Data and does not represent a virus hazard.
16. Consultation, Rectification and Claims Procedure
Truora has specific manuals designed for the procedure for queries, complaints and claims and for the Personal Data treatment procedure available here. Notwithstanding the foregoing, below is a brief summary of the procedures.
16.1. Query:
The inquiries and requests of the Data Owners will be attended within a maximum term of ten (10) business days, counted from the date of receipt of the same. In the event that it is not possible to resolve the query within this term, the Data Owner will be informed of said situation at the notification address that has been included in the respective query, and the response term may be extended for up to five (5) days. The response to the queries or claims that the Data Owners present may be delivered by any physical or electronic means.
16.2. Rectifications and Claims:
When the Data Owner considers that his information should be corrected, updated, or deleted, or when they notice an alleged breach by Truora of its duties regarding the Protection of Personal Data contained in the applicable legislation and in this Privacy Policy you may file a claim in the following ways:
-
- A written request must be submitted in response to the specific requirement.
- If the claim is incomplete, Truora will require the interested party to complete and correct the request, within five (5) days after receiving the request:
- If two (2) months elapse from the date of the request without the applicant having responded, the claim will be understood to have been withdrawn.
- If the person who receives the claim is not competent to resolve it, he will transfer it to the person who can solve it within a maximum term of two (2) business days and will inform the applicant of this fact.
- If two (2) months elapse from the date of the request without the applicant having responded, the claim will be understood to have been withdrawn.
- If the claim is received in full or has been completed later, within the following two (2) business days, a "legend" must be included in the database that indicates "CLAM IN PROCESS".
- Truora will resolve the claim within a maximum term of fifteen (15) business days counted from the day following its receipt. In the event that it is not possible to resolve the query within this term, the Data Owner will be informed of the delay, the reasons, and the date of response to the address of notification included in the respective claim. In any case, the response term may not exceed eight (8) business days following the expiration of the first term. The response to the claims that the Data Owners present may be made by any physical or electronic means.
- A written request must be submitted in response to the specific requirement.
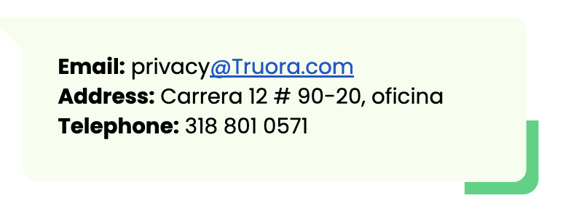
17. Data Protection Contact
Truora has created an area exclusively designated for the handling of Personal Data called Privacy Truora as responsible for the protection of your data, in the event of any doubt or concern about this Privacy Policy or the Treatment and use of Personal Information please Direct your queries, requests, complaints or claims to:
18. Deletion of Information
Any information storage device, which by definition of the Data Owner of said information, has lost its validity or has been withdrawn, must be safely eliminated in the terms established in the Manual of Procedures for Collection, Storage, Use, and Deletion. Information and the following aspects:
18.1. Removal Procedure
-
- The files will be stored for as long as the Data Owner requests it, being previously communicated by written communication addressed to the information security committee.
- In an extraordinary way, the partial or total elimination of the information of the Data Owner may be requested, which will affect both the files received, as well as all the data subsequently generated as a result of the management and Treatment carried out by Truora. For this, it is necessary to send a request to the Truora Privacy area, which will analyze if there is any legislation that does not allow its elimination or conservation for a period of time. In case of proceeding, the Truora Privacy area will request the OSI to eliminate the information from Truora´s databases.
- When proceeding to the elimination or destruction of personal information, the elimination act must be drawn up, with the signature of the areas present and involved in the process and detailing the fields that were proceeded for its destruction, in any case, Truora will keep the Personal Data of a public nature, for purposes of traceability of the information.
- Magnetic (electronic) media must be destroyed before disposal, ensuring that they cannot be read by third parties.
- In the case of decommissioned computers, their hard drive must be formatted or destroyed, so that the information stored, and the installed software are logically and physically removed from the equipment.
- Documents to be eliminated must be destroyed by means of paper shredding equipment, which must be enabled in suitable locations inside the Truora offices.
18.2. Destruction of backup media
-
- Physical Media: These types of media are physical representations of data, usually associated with hard copies (either handwritten or printed), plastic payment cards, FAX, photos, tapes, drums, plates, and printing plates, as well as any other physical device that serves as support for the storage of logical data, among which are:
- Magnetic media: floppy disks, hard drives, magnetic tapes, etc.
- Optical media: CD, DVD, etc.
- Magneto-optical media: Zip disks, Jaz disks, Super Disk, etc.
- Electronic media: Flash memories, ROM and RAM memories, solid-state drives (SSD), etc.
- Logical means: In this type of media, the logical representations of the data are stored in the form of bits and bytes and their corresponding structures (files, filesystems, units, etc.).
- Physical Media: These types of media are physical representations of data, usually associated with hard copies (either handwritten or printed), plastic payment cards, FAX, photos, tapes, drums, plates, and printing plates, as well as any other physical device that serves as support for the storage of logical data, among which are:
18.3. Deletion of Logic data
-
- Redact: This technique is used to remove certain parts of a digital document to prevent the display of sensitive data during a declassification process, including the deletion of the metadata and the removal/truncation of images and text.
- Delete: This technique simply performs a simple deletion of the reference to files at the operating system level (de-indexing), but their data remains on the storage medium and can be obtained again using forensic computing techniques.
- Clean: This method uses logical (software-based) procedures to securely erase data in storage locations to prevent such data from being recovered using computer forensic techniques. Usually, such secure erase procedures are applied through standard read/write commands on the storage device using data overwriting with a new value in several passes or applying factory default values (where overwriting is not supported). Use a secure erase tool that implements at least one overwrite pass.
- Purge: This method uses physical or logical techniques to prevent the data on the storage device from being recovered using laboratory techniques (for example recovery through magnetic remanence), especially when said device will be reused, recycled, or discarded. It is recommended to use at least one degaussing or purging equipment.
18.4. Deletion of physical data
-
- Redact: This action applies to written physical media and consists of sanitizing/truncating certain parts of a document in order to prevent potential disclosure of confidential information (declassification).
- Destroy: This last method eliminates the data by physically destroying the medium that stores it, leaving this support unusable, using techniques such as disintegration, incineration, pulverization, grinding or melting. The NSA publishes a list of approved products for physical destruction. It is recommended to use at least a destruction device with security level 3 (DIN).
- Redact: This action applies to written physical media and consists of sanitizing/truncating certain parts of a document in order to prevent potential disclosure of confidential information (declassification).
19. Modifications of the Privacy Policy
Truora is fully empowered to modify this Privacy Policy. Any changes will be published on our website and/or mobile applications. The granting of the Authorization, whatever its means, will be understood as an express manifestation of the acceptance of this Privacy Policy. It is the Data Owner's responsibility to frequently review these Privacy and Personal Data Protection Policies.
20. Validity
This Privacy Policy is effective as of June 1 of 2022 and will be reviewed periodically in the second week of March of each year.
21. Authority of issuance, revision, and publication
This Privacy Policy has been developed by our Privacy Truora area led by Gabriela Cala - Legal Counsel, this area is exclusively responsible of the protection of Personal Data and ensuring the exercise of the rights of the Data Owners. The Privacy Policy was approved by David Alejandro Cuadrado Cabrera - CTO/OSI.
Confidential August, 2024
